Understanding What OpenDNS Is All About
There have been many threats that have evolved from COVID19, but one of the more recent ones has been that of capturing the network traffic of an unsuspecting victim and from there, redirecting them to a spoofed or illegitimate website. One may ask at this point how this is possible, given all of the layers of encryption and authentication that a business can implement in order to protect their network lines of communications.
This is all due to the inherent weaknesses of what is known as the “DNS System”.
What Are the Security Weaknesses of The DNS?
There are a number of blatant security holes and gaps with the DNS, which are as follows:
- Any requests that are transmitted to the DNS are sent over in a plaintext format and remains unencrypted. This means that the information/data that is transmitted can be seen literally by anybody, especially the Cyberattacker. The bottom line here is that if this is intercepted, it could result in a huge backdoor in which to leverage and deploy malicious payloads, such as that of Ransomware, Trojan Horses, and other forms of Malware. But it is not just the DNS Servers and the device of the end user that are at grave risk. Every other network node that is involved with transmitting the domain name are exposed as well, which can have a cascading effect.
- Because the DNS Resolution is done in an unencrypted fashion, all of the other intermediaries that are involved, especially that of the Internet Service Providers can capture this data for covert surveillance of the end user.
- As stated earlier, the DNS is also very much prone to Spoofing. For example, a firewall or router that has been misconfigured or that has been tampered with intentionally, can quite easily modify or replicate the request sent over by the end user. Thus, the DNS may not even receive this at all, and instead, the end user will be directed to a spoofed website that looks almost like the real website that he or she was trying to access in the first place.
1. Migrating a traditional Claims Processing system into a more modern Web/Mobile front facing application:
A Solution to The Weaknesses – The Use of OpenDNS
This used to be the name of an actual company, and back in November 2012, they created a product known as “Umbrella”. In its first inception, it was designed for the IT Security teams across Corporate America to help enforce their respective Security Policies for those employees that were constantly on the go. This was done by implementing specific controls at the granular level in order to protect the flow of network communications to and from the corporate server, and vice versa, where the shared resources were accessed from. Further enhancements were made to Umbrella, which are as follows:
- Security Graph:
This makes up the concepts of Artificial Intelligence (AI), and it actually serves as a dynamic engine functionality in order to update the various blacklists that were created by Umbrella, which are as follows:
-
- The various types of Malware;
- Botnet attacks;
- Any known Phishing Domains;
- Any known malicious IP Addresses.
- Investigate:
This is yet another add on to Umbrella which gives the IT Security the ability to compare network traffic that originates from their company to that of what is transpiring on a global basis. Because of this, it has become much easier to analyze any pending Cybersecurity threats and prioritize them from high risk to low risk.
- The Intelligent Proxy:
This was added as an extra layer of protection so that Umbrella could literally have a second mechanism at hand in order to process those domain names that were deemed to be suspicious or malicious in nature as deemed by the Security Graph.
But on August 27th, 2015, Cisco purchased OpenDNS and the Umbrella product in an all cash deal estimated to be at $635 Million. From this point, Umbrella was rebranded as “Cisco Umbrella”, and kept all of the functionality in it, as described.
Other Functionalities of the OpenDNS
Ever since the buyout from Cisco, there have been more components that have been added to the OpenDNS. For example, it has added more servers on a worldwide basis, so that the nearest server can be located in order to process and complete the requests made by the end user, mostly when it comes to accessing different websites.
This actually helps to avoid any bottlenecks in the flow of network communications, and thus, lead to greater optimization, speed, and efficiency when the websites are being loaded up on the device of the end user.
It also adds more layers of security, in terms of detecting spoofed websites, and directing the end user to real, legitimate one. For example, it has a dedicated service called “PhishTank” that exclusively filters for those IP addresses that are known to be associated with Phishing based websites. Because of this, there is a lesser probability that you will access a malicious site.
Also, granular level parental controls have also been added so parents can keep a close eye on the Internet activities of their children, by allowing them to filter for the specific content of the websites that they are visiting, from 60 different categories.
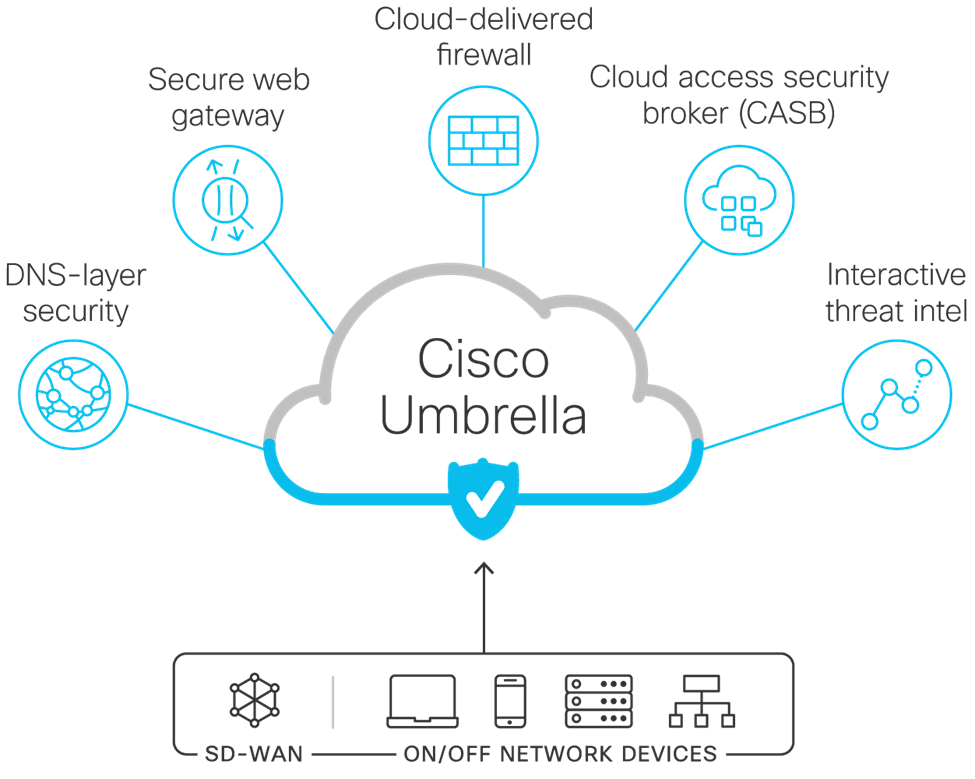
OpenDNS also operates as a:
- DNS Layered Security Agent:
You can further enhance your company’s security visibility, get real time updates on compromised systems that reside in your Network Infrastructure, and stop other kinds of threat vectors such as Ransomware, Botnets, and other forms of online attacks.
- Secure Web Gateway:
This makes use of what are known as “IPsec Tunnels”, to forward any network activity that is deemed to be malicious in nature, into another Cisco based proxy server located in the Cloud. This is used to further enforce those policies that are related to acceptable Internet usage standards, as mandated by your company.
- Firewall:
All networks originating from suspicious IP addresses are blocked and stored in system logs for further analysis and review.
- Cloud broker:
This allows for those non approved Cloud applications to be revealed, thus decreasing the impacts of Shadow Management occurring in your organization.
- Threat Intelligence gathering tool:
This collects information and data on a real time basis at it relates to spoofed websites, domain names, and IP addresses. This all available through a centralized console, thus allowing the IT Security team to respond in a much quicker manner to just about all types of threat variants that inbound into your Network Infrastructure.
- Integration between Umbrella and Software Defined Wide Area Networks (SD-WANS):
This is especially useful for protecting your remote and/or virtual offices, your employees, and all of the wireless devices that are used by them from any sort of Cyberattack.
All of this can be seen in the illustration below:
(SOURCE: 1).
Conclusions
Overall, this article has examined some of the major security vulnerabilities of the DNS system, and how the OpenDNS can help to overcome them. At KAMIND IT, we offer Cisco Umbrella to our clients, and if you are interested in learning more about it or are considering deploying it for your business, contact us today.
Sources
https://umbrella.cisco.com/products/cloud-security-service
https://en.wikipedia.org/wiki/OpenDNS
https://www.techopedia.com/definition/31257/opendns
https://www.netsec.news/opendns-web-filter-review/