
Introduction
In dealing with today’s Cybersecurity threat landscape, businesses and corporations have deployed many tools from different vendors to beef up their lines of defense. The thinking here is that more is better, but this is only increasing the attack surface for the Cyberattacker. There is now a fundamental shift in this kind of thinking, and CIOs and CISOs are starting to realize the importance of conducting security assessments to strategically place their tools.
But until this is fully realized, the IT Security staffs at these organizations are continuously inundated with a lot of information and data that they must parse through. It can take hours if not days to filter through all of this.
What would be nice is to have is a software package that can collect all this information and data and displace it into one central repository, using dashboards so that this can all be seen in one view. This is where the role of the SIEM comes into play.
The SIEM
Typically, this is the amount of information and data that an IT Security team deals with daily, which is represented in the matrix below:
The Security Stack
(SOURCE: 1)
The SIEM (which stands for Security Information and Event Management) is an application that takes all the above and brings it down into one view (or even multiple views, depending upon the security requirements of the organization). Also, it can quickly capture any sort of abnormal or anomalous behavior in real time, and immediately notify the appropriate personnel about it. At its core, the SIEM can be thought of as a data aggregator that collects information from all the tools that are displaced at a business entity. This includes such as items as the network devices (such as the Routers, Firewalls, Network Intrusion Devices, etc.), Servers, and the Domain Controllers. It also allows for the Cybersecurity Analyst to conduct forensic like research into security breaches that may have occurred.
How A SIEM Works
The diagram below illustrates the process as to how a SIEM works:
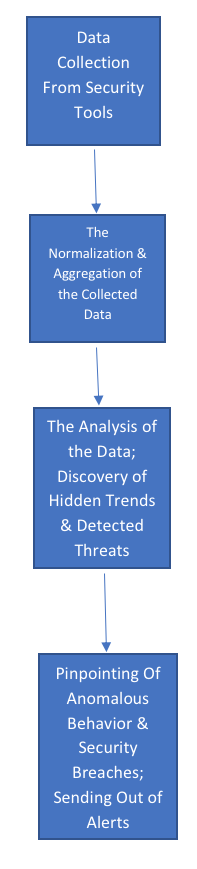
(SOURCE: 2)
The Functionalities Of a SIEM
A SIEM possesses the following functionalities:
- Event and Log Data Capture:
The SIEM can be highly customizable in terms of the information and data that it collects, and only the most relevant pieces will be displayed. All of this is stored into one central repository, which allows for the business entity to come into compliance with regards to storage requirements. - Concise Views:
As described earlier, the SIEM presents a “birds’ eye” view of what is transpiring. These views or dashboards can be custom created in order to meet the specific needs of the IT Security staff. An example of this can be seen in the illustration below:
(SOURCE: 1)
- Normalization:
This involves two separate parts:- Breaking down all the techno jargon into a format that can be quickly and easily understood;
- Mapping the data fields as established by the vendor to that of the end user (this is also referred to as Field Mapping”).
- Correlation
Past trends can be matched up to new ones that have been discovered, thus providing a real sense of what is happening. - Scalability:
A SIEM software application can be quickly ramped up or down, depending upon the changing needs of the organization. A typical example of this is when more intelligence feeds are plugged into the SIEM, so that it can “learn” and predict into the future. - Reporting:
Continuous monitoring is available, 24 X 7 X 365.
Conclusions
Overall, this blog has provided an overview into what a SIEM is, and what it can do. It can be deployed either as an On-Premises solution or in the Cloud (this is known as “SIEM as a Service”). If you choose the former, you will be responsible for the installation and ultimate maintenance of the software package. But if you choose the latter, it is up to the Cloud provider to do all of that. Some of the key benefits of SIEM as a Service include the following:
- Managed Service Delivery: The Cloud provider can help you with the configuration and fine tuning of your SIEM package;
- More Deployment Options: This means that you have greater flexibility as to how and where you want your SIEM package to be deployed;
- Flexible Pricing: By using a Cloud based approach, your pricing will become fixed, and best of all, affordable to any IT budget.
Sources



 (SOURCE: 1)
(SOURCE: 1)

