On October 1st of this year, Microsoft will turning off all old legacy security protocols for Exchange Online. These are technically known as “Basic Authentication.” These are some of the oldest authentication and authorization protocols that have been used, and because of the changing dynamics of the Cyber threat landscape, they simply cannot provide the protection that businesses need today.
On October 1st of this year, Microsoft will turning off all old legacy security protocols for Exchange Online. These are technically known as “Basic Authentication.” These are some of the oldest authentication and authorization protocols that have been used, and because of the changing dynamics of the Cyber threat landscape, they simply cannot provide the protection that businesses need today.
So in response, these security protocols will be deprecated in order to mitigate the risks of any large-scale security breach happening through the Exchange platform.
But it is important to note at this point that Microsoft will not just do a massive shutdown for all users on October 1st. Rather, they will used a phased approach. For example, certain users will be selected at random, and they will be given a 7-day notice about the permanent shutdown.
This process will still continue in a random fashion until the end of 2022, when it is expected that all legacy protocols will be entirely eliminated for all users, on a global basis. The following security protocols are the ones that will be disabled under the “Basic Authentication” umbrella:
- MAPI
- RPC
- Offline Address Book (OAB)
- Exchange Web Services (EWS)
- POP
- IMAP
- Exchange ActiveSync (EAS)
- Remote PowerShell
While Microsoft strongly suggests that end users also disable the SMTP AUTH protocol, it will not be eliminated for those that are still actively using it. If you must continue to use this, it is highly recommended that you keep it active at only the least minimal conditions that are required for it. But this protocol will be eliminated for those end users that have not used it at all.
How Do I Know If I Am Using Basic Authentication?
The first person you should turn to in this regard is your network administrator. Or, if you have your Exchange Online account through a Cloud Services Provider (CSP), of the support engineers should be able to answer this question for you. But as you are waiting for a response, there are some simple checks that you can do yourself. Here is just a sampling:
1. Check the Authentication Dialog Box:
If you have what is known as “Modern Authentication” enabled, your login screen should like this:
However, if you are still Basic Authentication, your login screen will look like this:
(SOURCE: 1).
2. Check the Connection Status:
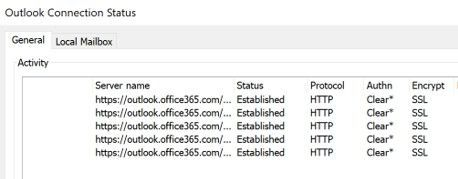
If you are using Basic Authentication, the value of “Clear” will appear in the Outlook Connection Status dialog box:
(SOURCE: 1).
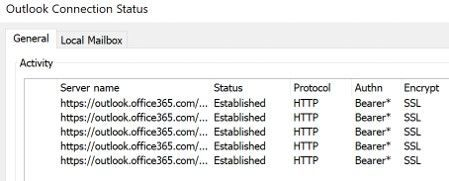
But, if you are using Modern Authentication, the value of “Bearer” will appear:
(SOURCE: 1).
3. Check the Message Center:
If any of your end users are still using Basic Authentication, you will receive notifications directly from Microsoft as those accounts that still have it enabled. Of course, if you don’t receive any messages, then you are either using Modern Authentication or Basic Authentication has been automatically turned for you by Microsoft. In either case, it is important to keep checking your Message Center on a regular basis.
4. Check the Administration Center:
View the summary usage reports, as this will include those protocols that are either enabled or disabled.
5. Check the Azure Active Directory:
This is the best place to confirm if you are using Basic Authentication or not, by using the Sign In Report which is provided. If you are unfamiliar with this process, click here to get more information in how to do this.
How To Be Proactive
If after you have discovered that you are running Basic Authentication, and want to disable it yourself, follow the table below. Note that there are advantages and disadvantages to each kind of approach, so it is best to consult with your Cloud Service Provider (CSP) first.
|
Method |
Pros |
Cons |
|
Security Defaults |
- Blocks all legacy authentication at the tenant level for all protocols |
- Cannot be used together with Azure AD Conditional Access policies |
|
Exchange Online Authentication Policies |
- Allows for a phased approach with disablement options per protocol |
Admin UI available to disable basic authentication at org-level but exceptions require PowerShell |
|
Azure AD Conditional Access |
- Can be used to block all basic authentication for all protocols |
- Requires additional licensing (Azure AD P1) |
(SOURCE: 1).
Conclusions
Although this blog has provided some tips and recommendations to follow, trying to disable Basic Authentication can still be a complex process. If you have any questions or need any kind of help, contact us today.